Practical Security Analysis from the Field
Deep examinations of industry incidents, vendor risk, and operational security decisions – no certifications required, just 25+ years of experience.
After twelve weeks exploring the realities of security work, this piece reflects on the lessons that only experience teaches—organizational dynamics, pragmatic trade-offs, and how to build a sustainable security career in imperfect environments.

Every public breach is a free lesson—if you know how to read it. This piece explains how to extract meaningful, transferable insights from breach disclosures, avoid threat inflation, and apply patterns to your own environment without relying on hindsight or headlines.

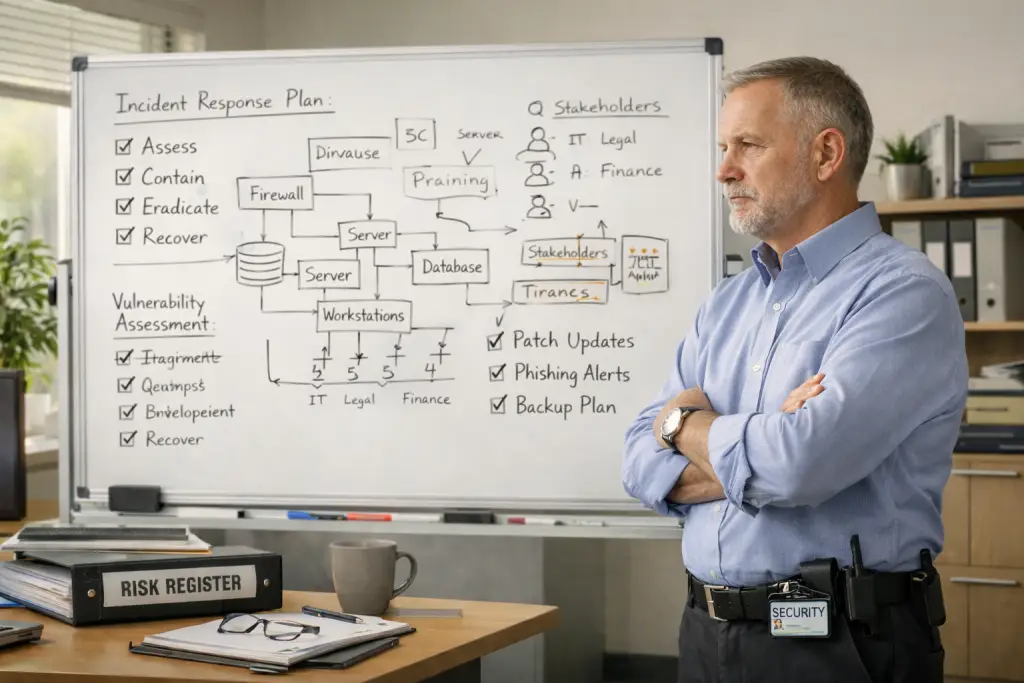
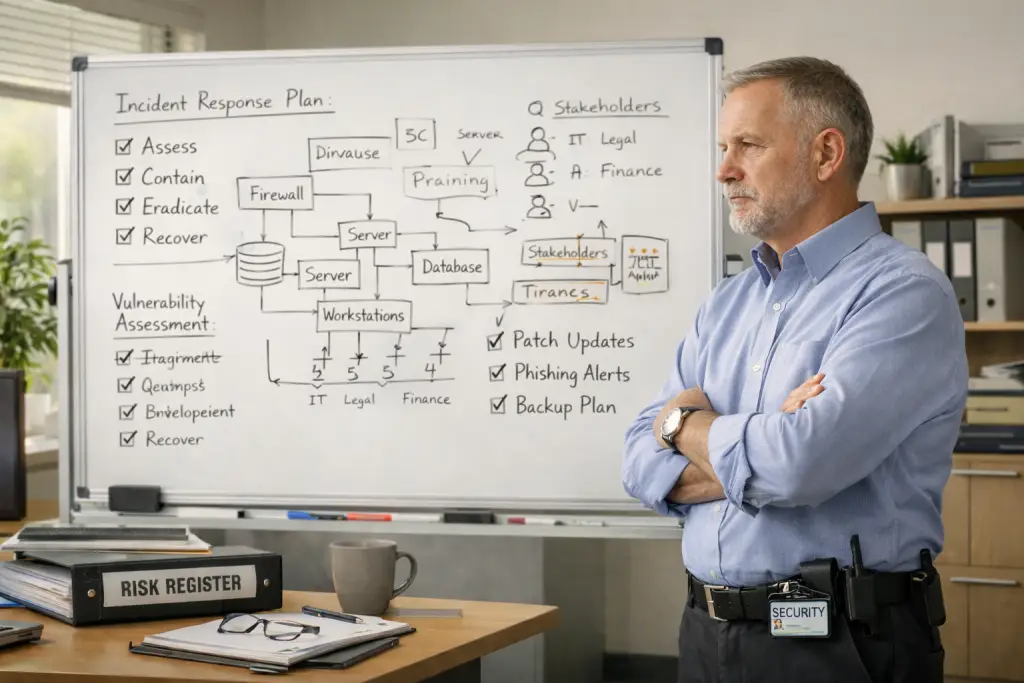
Most incident response plans assume clean timelines and clear answers. Real incidents are messier—shaped by uncertainty, executive pressure, incomplete data, and human dynamics that matter as much as technical skill.
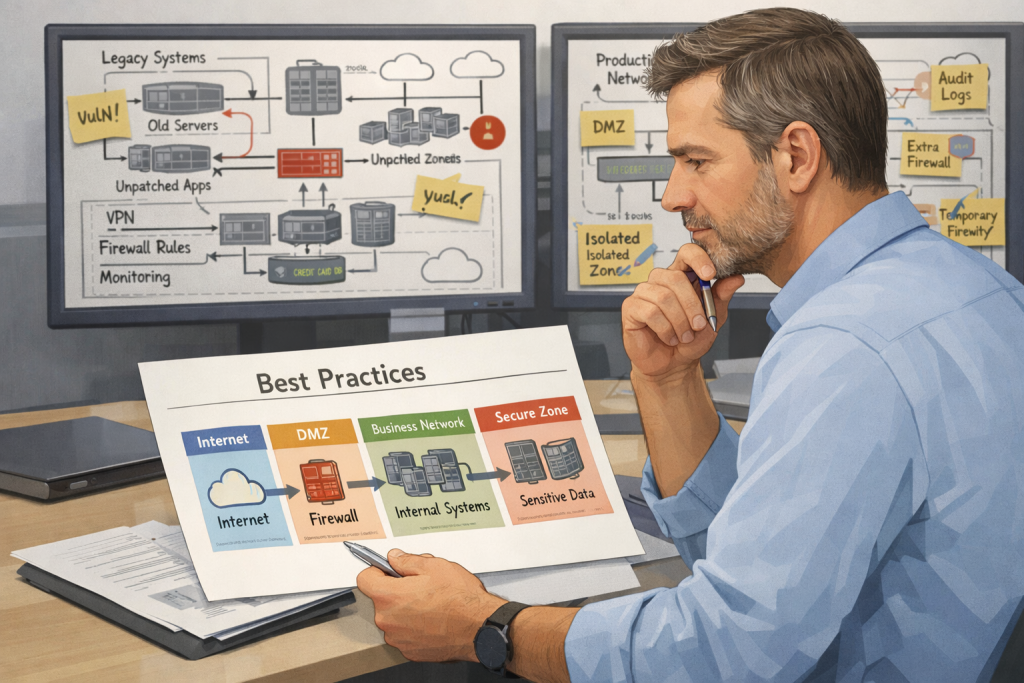
Best practices assume ideal conditions. Real security work rarely has them. This post explores how experienced practitioners apply judgment, weigh trade-offs, and decide when “good enough” is acceptable—and when it isn’t.
Passing an audit feels like progress—but it often masks real security gaps. This post explores why compliance is a baseline, not a strategy, and how security leaders can navigate audits without letting them define their security program.

Security work doesn’t fail because it’s wrong—it fails because it’s misaligned. This post breaks down what CISOs are actually accountable for, how pressure shapes priorities, and how to align security work with the realities of leadership decision-making.
After twelve weeks exploring the realities of security work, this piece reflects on the lessons that only experience teaches—organizational dynamics, pragmatic trade-offs, and how to build a sustainable security career in imperfect environments.

Every public breach is a free lesson—if you know how to read it. This piece explains how to extract meaningful, transferable insights from breach disclosures, avoid threat inflation, and apply patterns to your own environment without relying on hindsight or headlines.

Most incident response plans assume clean timelines and clear answers. Real incidents are messier—shaped by uncertainty, executive pressure, incomplete data, and human dynamics that matter as much as technical skill.
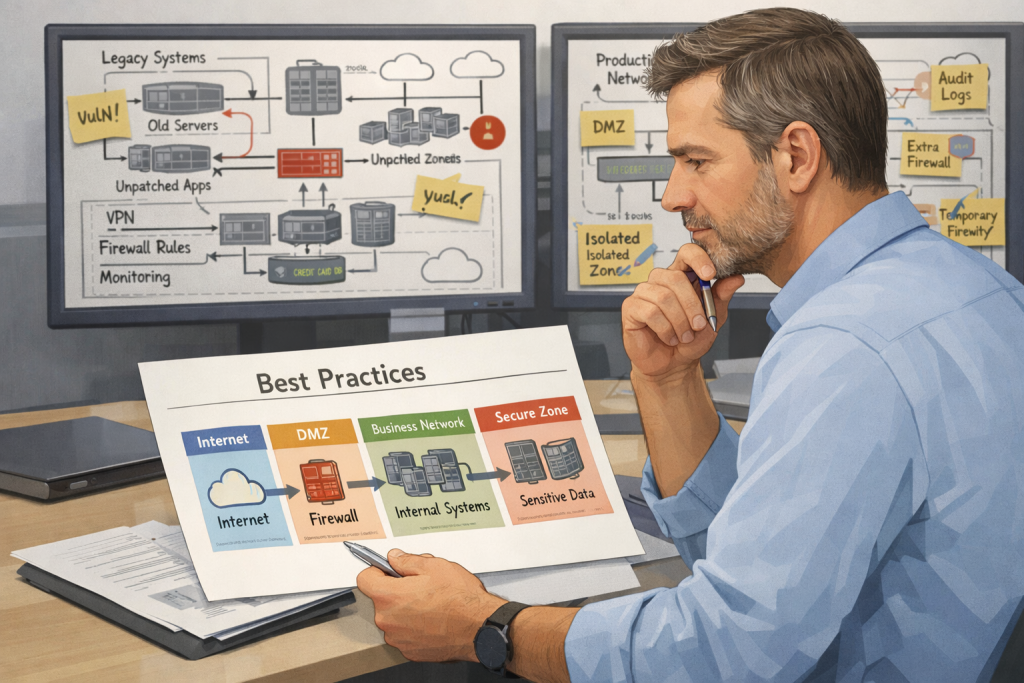
Best practices assume ideal conditions. Real security work rarely has them. This post explores how experienced practitioners apply judgment, weigh trade-offs, and decide when “good enough” is acceptable—and when it isn’t.
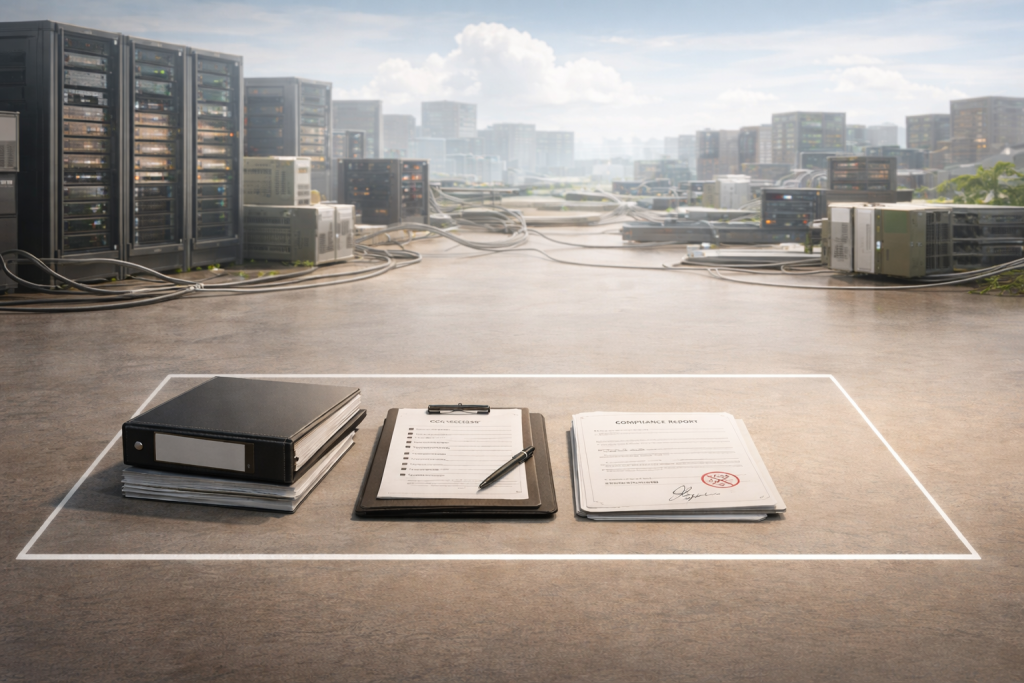
Passing an audit feels like progress—but it often masks real security gaps. This post explores why compliance is a baseline, not a strategy, and how security leaders can navigate audits without letting them define their security program.

Security work doesn’t fail because it’s wrong—it fails because it’s misaligned. This post breaks down what CISOs are actually accountable for, how pressure shapes priorities, and how to align security work with the realities of leadership decision-making.
After twelve weeks exploring the realities of security work, this piece reflects on the lessons that only experience teaches—organizational dynamics, pragmatic trade-offs, and how to build a sustainable security career in imperfect environments.
Every public breach is a free lesson—if you know how to read it. This piece explains how to extract meaningful, transferable insights from breach disclosures, avoid threat inflation, and apply patterns to your own environment without relying on hindsight or headlines.
Most incident response plans assume clean timelines and clear answers. Real incidents are messier—shaped by uncertainty, executive pressure, incomplete data, and human dynamics that matter as much as technical skill.
Best practices assume ideal conditions. Real security work rarely has them. This post explores how experienced practitioners apply judgment, weigh trade-offs, and decide when “good enough” is acceptable—and when it isn’t.
Passing an audit feels like progress—but it often masks real security gaps. This post explores why compliance is a baseline, not a strategy, and how security leaders can navigate audits without letting them define their security program.
Security work doesn’t fail because it’s wrong—it fails because it’s misaligned. This post breaks down what CISOs are actually accountable for, how pressure shapes priorities, and how to align security work with the realities of leadership decision-making.
